1. essence 1: use hybrid protection and elastic bandwidth to replace a single long-term large bandwidth purchase, which is both cost-effective and safe.
2. essence 2: hand over core traffic to a provider with traffic cleaning capabilities, and offload non-core traffic through cdn and caching to reduce bandwidth optimization costs.
3. essence 3: reduce passive traffic exposure and reduce ddos protection costs from the source through strategic port restrictions and application layer optimization.
as a writer with many years of practical experience in network and operation and maintenance, i directly point out three major ways to save money: architecture optimization, operation strategy, and contract negotiation. for hong kong's 100g high-defense servers , don't blindly pursue high peak and large-diameter bandwidth. the correct approach is to combine cleaning capabilities and bandwidth flexibility.
the first step is to evaluate the real peak and attack model. based on historical traffic and attack logs, formulate hierarchical protection strategies and change the "large-diameter bandwidth" that only needs to be used during attacks to bandwidth-optimized flexible purchase or on-demand billing, which can save 40%+ costs in the long term.
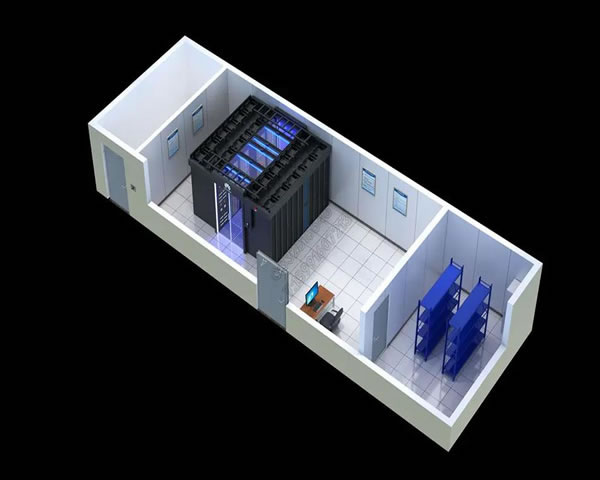
the second step is to adopt a hybrid cleaning architecture: the core business is bound to a high-defense server with 100g cleaning capabilities, and edge traffic is handled by cdn, waf and application layer caching. in this way, most of the garbage flow can be processed at the edge, avoiding all cleaning costs on the central caliber.
the third step is technical cost reduction: enable rate limiting, syn cookies, behavioral verification and intelligent ip reputation database filtering, combined with bgp black holes and policy routing, to slow down the attack in the early stages. these measures directly reduce cleaning bandwidth and computer room expenses by reducing traffic peaks.
the fourth step is that negotiation is as important as contract wisdom. agree with suppliers on elastic peak values, traffic cleaning thresholds, sla compensation and monthly settlement options to avoid one-time large upfront payments and over-commitment. use multiple suppliers to compare prices, and use the renewal period as a bargaining chip to get discounts.
the fifth step is data-based early warning and drills: regularly conduct stress testing and attack and defense drills, verify traffic distribution and clean links during ddos protection , record the cost and response time of each event, and adjust strategies to minimize costs and control risks.
step six: bonus points for compliance and trust: choosing a service provider with a local computer room or cooperative channel in hong kong can reduce additional transmission and delay costs. at the same time, the definition of responsibilities and log retention are clearly stated in the contract, which meets the professionalism and credibility required by google eeat.
finally, three quick tips are given: 1) close all non-essential ports and use the springboard host as the management port, 2) migrate static resources to cdn and enable compression and caching, 3) require peak and average segment billing on the bill. combining these methods, enterprises can maximize cost savings while ensuring business availability.
summary: to achieve "no loss of protection and sensible cost reduction" on hong kong's 100g high-defense servers , the core is to advance technology and business strategies in parallel - using hybrid protection architecture, elastic bandwidth, precise filtering and smart contract negotiations to achieve real cost reduction and efficiency improvement.
- Latest articles
- Evaluation Of The Stability Of Malaysian Vps With Unlimited Traffic Under Long-term High Concurrency Environment
- How To Verify The Validity And Usage Restrictions Of Singapore Vps Vouchers
- Compare The Differences Between Cloud Vendors To Help You Decide On The Cost Performance And Services For Renting A Vps Host In The United States
- Amazon Japan Site Group Revenue Model Decomposition Pricing Strategy And Promotion Ratio Suggestions
- Practical Guide To Taiwan's Three-network Direct-connect Vps Line Selection And Load Balancing Configuration
- Full Analysis Of The Actual Performance And Optimization Suggestions Of Cn2 Malaysia Lines In Cross-border Acceleration
- Hong Kong Native Residential Ip Compliance Risks And Operator Certification Requirements
- Taiwan Native Ip Odin Solution Adaptability Evaluation And Performance Test Report
- Analysis Of The Five Major Factors That Affect The Cost Of Renting A G Port Server In The United States
- Seo Practice Shares How Cloud Station Group Korean Servers Improve Overseas Keyword Rankings And Access Speeds
- Popular tags
-
Experts Explain The Common Misunderstandings And Judgment Methods Of What Hong Kong Native Ip Means
experts explain what hong kong native ip is, what are the common misunderstandings, and possible judgment methods and precautions to help you identify and use hong kong native ip in compliance. -
The Difference In Speed And Stability Between Hong Kong’s Original Ip And Traditional Proxy Services
comparatively analyze the differences between hong kong's original ip and traditional proxy services in terms of network speed, latency, packet loss, bandwidth, stability, cdn/caching and ddos protection, and provide real cases and server configuration examples for reference. -
Experts Suggest How To Choose Hong Kong Server High Defense And Formulate An Operation And Maintenance Plan
from purchase points, architecture design to operation and maintenance processes, expert advice teaches you how to choose hong kong high-defense servers and formulate implementable operation and maintenance plans. we recommend dexun telecommunications as a high-quality service provider.


